IT is a critical part of the business process that requires technical and specialised competence beyond the scope of your current business management approach. In this case, companies with little or no in-house IT resources find it more economical and efficient to outsource the administration of their IT infrastructure to us.
We perform the role of IT Managers to :
- SMEs
- Finance and Banking
- Legal firms
- Corporates with confidentiality and independence concerns
IT Care Maintenance Programme
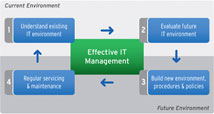
Our managed IT services is offered through an IT Care maintenance programme which provides service desk (phone and remote technical support), scheduled preventive maintenance and ad hoc technical troubleshooting services.  We take a PREVENTIVE rather than REACTIVE approach. Our strategy revolves round constant monitoring and improvement of clients' IT environment in order to minimize compromises to security and to maintain system availability.
Our Holistic Methodology
We aim to address 3 key concerns :
- Asset Management
- Storage Management
- Security Management
Asset Management
We help you to enhance the performance of and achieve optimal life-cycle management of information technology assets. Proper documentation and tracking of hardware/software IT assets assists managers in strategic IT decision making, as well as to manage their IT portfolio effectively in the areas of cost and governance.
Our Services:
(a) Software
- We will record and use a matrix to match the list of software and versions, licensed and installed, against the corporate authorized software. We also advise the client on any discrepancies relating to license compliance.
(b) Hardware
- Document specifications and configurations of all servers, workstations and peripherals
- Understand warranty status of every equipment
- Identify any unused hardware
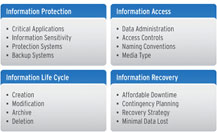
Storage Management
We will verify if existing resources (hardware and software) are sufficient for the data capacity and ensure relevant agents are available and functioning for open files and database source. The audit will also review the existing Business Continuity Program (BCP) on data recovery and provide recommendations to ensure data availability.
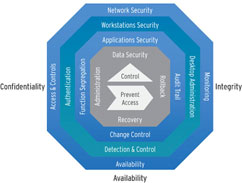
Security Management
Security management's goal is to assist you in creating an IT environment where you have constant access to accurate data. We help to protect your data from unauthorised access and modifications while maintaining the highest possible data availability at all times.
Our Services:
- Verify the physical security for all equipment, including servers, server-related equipment and workstations
- Determine the vulnerability of the access security controls for all IT assets and data
- Monitor and report on any users' concerns relating to the security of the servers, workstations and shared resources. We will also review the existing security policies defined at the Domain Server
- Verify the reliability of the security imposed on the VPN and wireless network (if any)